When you’re working with client information, you don’t want everyone to see everything. You want people to have enough access to do their jobs, and no more.
Understanding and using User Roles and Permissions can help you manage this easily.
This article, we’ll discuss how Gatheroo uses User Roles to give the right people, the right access – based on the way your business is set up.
We’ll explain:
- What the core roles are in Gatheroo
- How roles make it easier to control access to sensitive information
- How roles connect with request‑level access
If you’re looking for how to control access to a specific request, see the Control Who Sees Your Clients’ information in Gatheroo guide.
Why Roles Matter
Instead of managing access person by person, Gatheroo lets you group people into roles: Either “Owner”, “Admin” or “Member”, and control what each role can access.
By customising the account admin access you grant to “Admin” and “Member”, you can set Gatheroo up to efficiently grant the right access to the right people.
This makes it much easier to:
- Protect sensitive settings (like billing and domains)
- Limit who can change user access
- Support your internal security and governance requirements
- Scale as your team grows, without reconfiguring every user individually
Once set up, you assign each team member to the most appropriate role, and use these roles to set up your Request Templates to be visible to the roles who need them.
The Three Core Roles
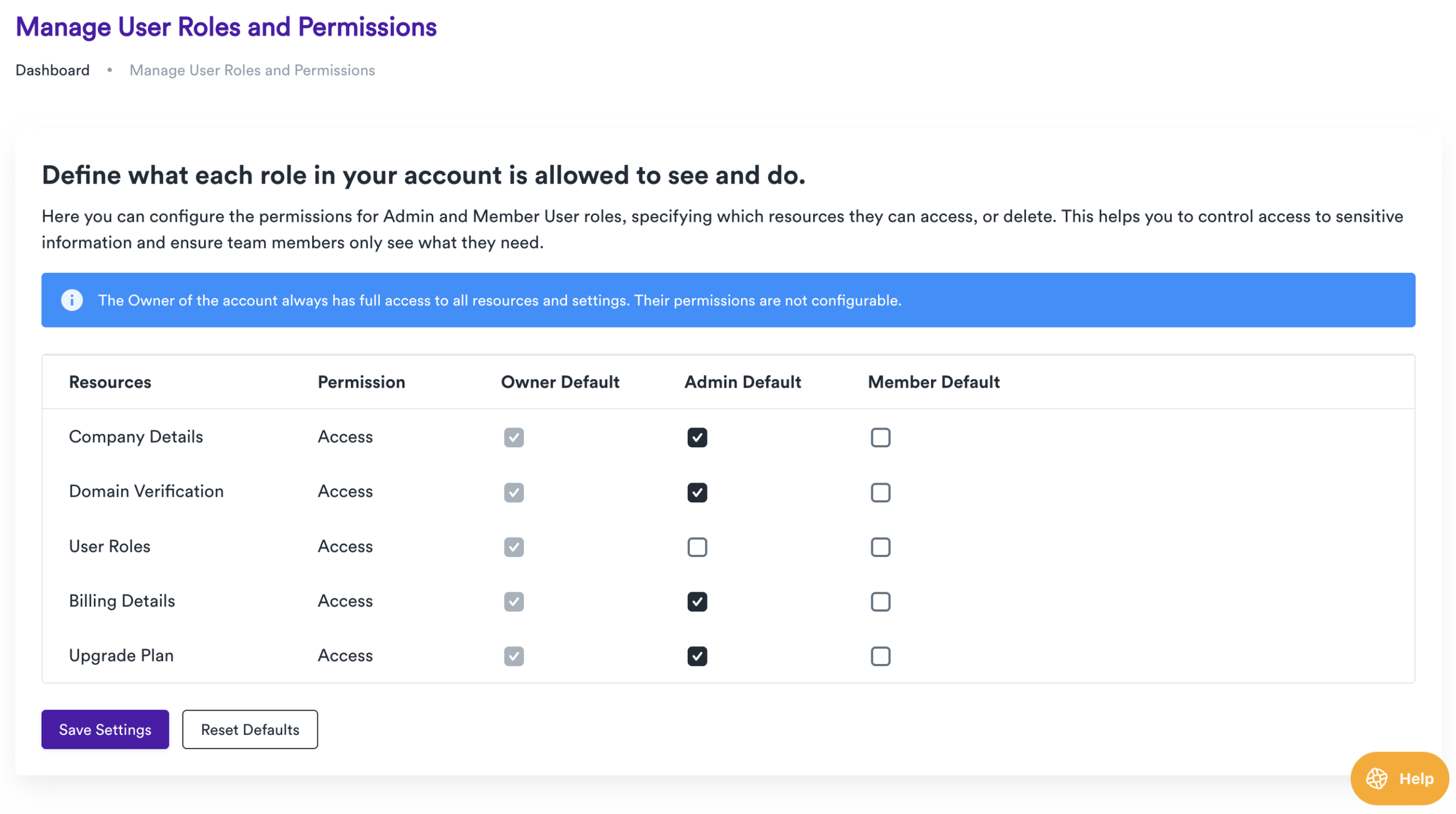
You’ll see three main roles on the Manage User Roles and Permissions screen:
Owner
- The account Owner always has full access to all resources and settings.
- Their permissions are not configurable from this screen.
- This is typically the person ultimately responsible for the subscription and security of the account.
Admin
- Admins are your trusted power users.
- They can usually manage most settings, users and account‑level configurations that the Owner delegates to them.
- They’re ideal for ICT managers, senior staff or team leads who need to maintain the system.
Member
- Members are your day‑to‑day users.
- They can work with clients, send requests and perform operational tasks, depending on how you configure their permissions.
- By default, they have less access to sensitive settings than Admins.
You control the difference between Admins and Members using permissions on specific resources.
The Owner column is there for completeness, but remember: the Owner always has full access.
How Roles Help You Protect Sensitive Areas
User Roles and Permissions are particularly useful for keeping high‑risk or sensitive areas under tighter control, such as:
- Billing Details and Upgrade Plan – you may only want the Owner and one or two Admins to change subscription or payment details.
- User Roles / Access Settings – you may want only the Owner and a trusted Admin to change who can see what.
- Company Details and Domain Verification – these often form part of your organisation’s security posture and branding.
A common pattern is:
Owner – full access to everything.
Admins – can manage most settings and users, but may be limited on billing or certain security‑critical areas depending on your policy.
Members – can work with client requests and data, but cannot touch billing, user roles or high‑risk configuration.
This keeps responsibility aligned with seniority and makes it easier for ICT or security teams to review who can change what.
How Roles Work With Request‑Level Access
Roles and permissions are your baseline.
They define what each type of user can generally see and do across the account.
Request‑level access then lets you apply finer control on a per‑request basis.
Together, they allow you to:
- Use roles to decide who could access certain types of information (e.g. only Owners and Admins can view certain areas).
- Use request‑level access to decide who can access each client request (e.g. only a specific account manager plus the Owner).
For example:
You set up your Request Templates to grant Admin Users access to all your client requests.
For a particularly sensitive request, you then set the request‑level access to just the Account Owner and one Admin.
If your roles are set up thoughtfully, managing request‑level access becomes much simpler and more predictable.
Your Member Users can set up requests on behalf of others, but they won’t get to see the client information unless you add them to the individual request.
Next: Controlling Access to Individual Requests
Once you’re comfortable with how roles and permissions work, the next step is to decide who can access each request.
Read next:
Control Who Sees Your Clients’ information in Gatheroo.