Email became the default way professional services businesses collect client information for one reason: it was already there. No decision was made. No process was designed. Clients were already using it, staff were already using it, and asking someone to attach a document to a reply was simpler than building something better.
That logic made sense in 2005. It creates real problems in 2026.
This post covers exactly what those problems are, not in abstract terms, but in the specific ways an email-based intake process fails the businesses that rely on it. And what the alternative looks like in practice.
The problem is not that email is unfamiliar
One objection comes up regularly when businesses consider moving away from email for client intake: clients are comfortable with it. They know how to attach a file. They do not need to learn anything new.
This is true. It is also not a good enough reason to keep using it.
The fact that a process is familiar does not mean it is fit for purpose. Email was built for communication. It was not built for structured information collection, identity verification, access control, or compliance record keeping. Using it for those purposes is not a workaround. It is a misapplication of the tool entirely.
What email-based intake looks like behind the scenes
When a professional services business collects client information over email, here is what is happening, whether the business is aware of it or not.
The information travels through servers your business does not control. A standard email message passes through multiple servers between the sender and the recipient. Your business controls its own mail server. It does not control any of the others. Neither does your client.
The information lands in an inbox with no access controls. Once a client’s passport, tax file number, bank statements or financial records arrive in your inbox, they are accessible to anyone with access to that inbox. In many businesses that means multiple staff members, with no record of who opened what or when.
The document gets downloaded, saved, and copied. It goes to a desktop. Then perhaps a shared drive. Then someone emails it to a colleague. At each step, a new copy exists somewhere, and the business has progressively less visibility over where the original information now sits.
There is no structured record of what was requested. When a regulator, auditor or senior manager asks what information was collected from a client, when it was requested, and when it was received, the answer lives in a search of the inbox. Which depends on nothing being deleted, threads not being fragmented, and someone having the time to piece it together accurately under pressure.
There is no guarantee of completeness. A client who receives an email asking for several documents will provide what they think you need. Sometimes that is everything. Often it is not. There is no guidance telling them exactly what format you need, what qualifies as acceptable, or what happens if something is missing. The follow-up is manual. The rework is absorbed by your team.
The specific risk in regulated industries
For professional services businesses operating in financial services, mortgage broking, legal, conveyancing and accounting, the stakes of getting this wrong are higher than they are for most.
Email interception fraud is a documented and growing problem in Australia. It is particularly prevalent in conveyancing and mortgage broking, where large sums of money change hands and clients are accustomed to receiving financial instructions by email. A fraudulent party intercepts an email thread, substitutes their own bank details, and the client follows the instructions believing them to be legitimate. By the time anyone realises the error, the funds are gone.
This is not a hypothetical. It has happened to businesses across Australia, at significant financial and reputational cost.
Beyond interception, the AML/CTF reforms commencing 1 July 2026 bring formal obligations for lawyers, accountants, conveyancers and real estate agents including documented client identity verification, structured record keeping, and the ability to demonstrate an auditable intake process to AUSTRAC. An email chain does not meet that standard.
What a structured client intake process looks like instead
The alternative to email is not a complex IT project. It is a purpose-built process that produces the security, structure and records that email cannot.
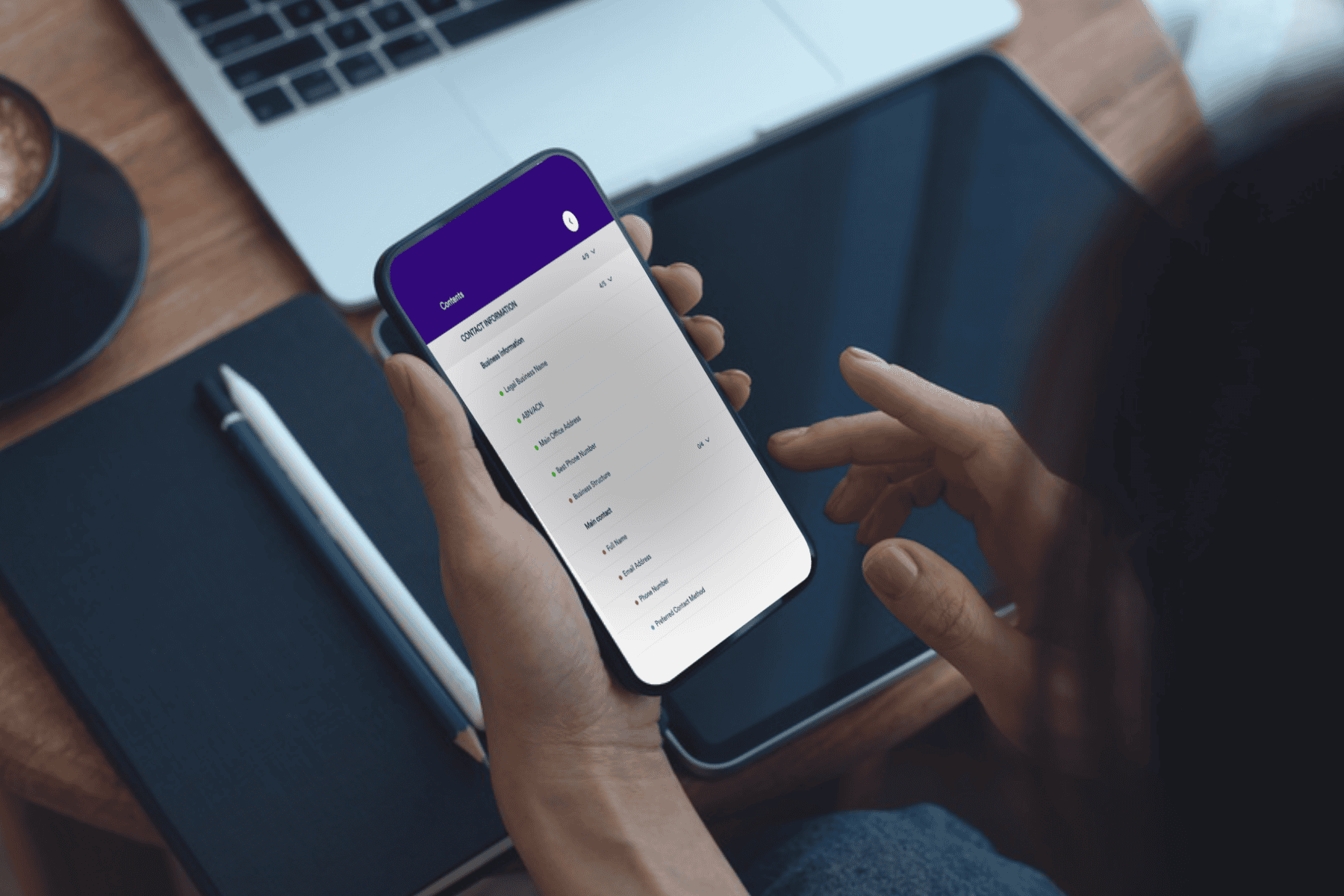
A consistent channel for every client. Information is collected through a secure portal. The same process, every time, for every client. There is no variation depending on which staff member sent the request or which client is involved.
Encryption from submission to storage. Every piece of information submitted through the portal is encrypted in transit and at rest. Australian data storage means the data is subject to Australian law and is not held on servers outside the country.
Guided intake that gets it right the first time. Structured fields, clear instructions, conditional questions and repeater fields mean clients provide exactly what is needed in the right format, with nothing missing. The chasing stops because the process removes the reason for it.
A record that builds itself. Every request generates a timestamped audit trail -> when it was sent, when it was opened, what was submitted, and when. No one has to document this manually. It exists as a natural output of using the right tool.
Identity verification without the retention risk. Clients submit identity documents through the portal. Staff view the document, mark it as verified, and delete it, without downloading it to any local device or drive. The audit trail records the verification. The document does not linger anywhere it should not.
Access controls that match your team structure. Sensitive requests are visible only to the staff members who need them. Role-based access means the right people see the right information and there is a record of who accessed what.
The real cost of the current process
The security risk gets the most attention when businesses consider moving away from email. It is a legitimate concern. But it is not the only cost.
The daily operational cost of an email-based intake process is real and largely invisible: the hour spent chasing the document that was not attached, the follow-up explaining what format you need, the request that came back incomplete again. None of that appears on an invoice. All of it is absorbed by your team, week after week.
A structured intake process eliminates that work. Not by adding more process, but by replacing a broken one with one that functions correctly from the start.
Three questions worth asking about your current process
If a regulator asked you to demonstrate your client intake process tomorrow, what would you show them? If the answer involves an inbox search and a folder of attachments, the process is not audit-ready.
Do you know where every piece of client information your business has collected in the last 12 months currently sits? If not, controlled retention and deletion is not possible.
Is the way your business collects client information consistent with the security standards you apply to everything else? If your internal data is protected and your intake process runs over standard email, the answer is no.
How Gatheroo addresses collecting client information
Gatheroo replaces email as the primary channel for collecting client information and documents with a secure, guided, auditable portal built specifically for Australian professional services businesses.
Every request is encrypted in transit and at rest. Data is stored in Australia. Two-factor authentication verifies client identity at the point of access. A full audit trail records every interaction automatically. Role-based access controls limit visibility to the right team members. And when information is no longer needed, deletion is complete, removed from our servers entirely.
Gatheroo helps businesses build a secure, auditable client intake process with Australian data storage, encryption, 2FA access control and a full activity trail supporting your obligations under Australian privacy and AML/CTF legislation.
A 14-day free trial is available with no credit card required. Most businesses have their first request sent within the same day.
Evaluating your options? See how Gatheroo stacks up against FileInvite -> two of the most common alternatives to email-based document collection.
Frequently asked questions
Why is email not secure enough for collecting client documents?
Standard email is not end-to-end encrypted. Messages pass through multiple servers outside your control during transmission, and your client’s inbox security is entirely beyond your reach. Once an email arrives in your inbox, there are typically no access controls governing who can view or download the attachment. For sensitive personal, financial or identity documents, this is not an acceptable standard.
What is the alternative to collecting client documents by email?
A purpose-built secure client portal – one that collects information through an encrypted, controlled channel, produces a timestamped audit trail, verifies client identity, and stores data in Australia under your governance. The process is consistent, documented, and does not depend on the security of your client’s email environment.
What are the compliance risks of using email for client intake in Australia?
The Australian Privacy Act requires businesses to take reasonable steps to protect personal information from misuse, interference and unauthorised access. For businesses captured under Australia’s AML/CTF regime including lawyers, accountants, conveyancers and real estate agents from 1 July 2026, there are additional requirements for documented client verification and structured record keeping. An email-based process is unlikely to satisfy either standard under scrutiny.
What is email interception fraud and how does it affect professional services businesses?
Email interception fraud occurs when a third party intercepts an email thread and substitutes fraudulent instructions – typically directing funds to a different account. It is a significant and growing risk in Australian conveyancing, mortgage broking and legal services. A secure client portal removes the vulnerability entirely by eliminating email as the channel through which sensitive instructions and documents travel.
How long does it take to move away from email-based client intake?
With the right tool, the transition is faster than most businesses expect. Gatheroo can be set up and sending your first structured request within the same day. The more meaningful shift is process – deciding what you need from clients, building it as a structured request, and making that request your new default. Most businesses are operational within a day and confident within a week.
Does switching away from email mean clients have to learn a new tool?
Clients receive a unique secure link by email and access a guided portal – no account creation, no passwords to remember, no software to install. The experience is designed to be clear enough that a client can complete it without any instruction from your team. In practice, clients often find it easier than piecing together what an email is asking them to do.
This article is general in nature. For advice specific to your obligations under Australian privacy law or AML/CTF legislation, we recommend engaging a qualified compliance professional.